Op-ed: DegenFi is Over
Long Live Decentralized Finance.
-Danger, Today in DeFi founder
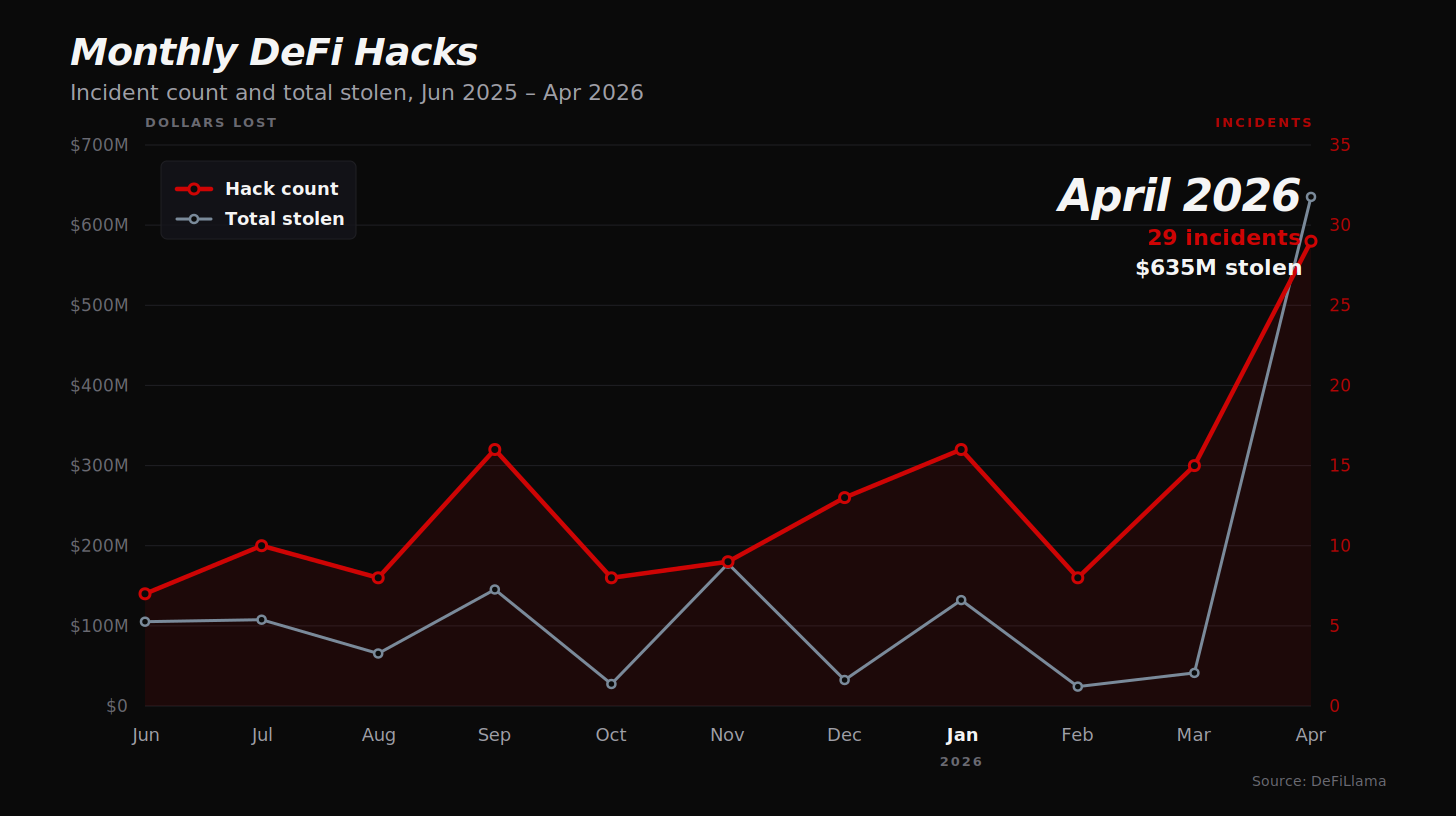
April 2026 logged 29 DeFi exploits and $635M in losses. That’s about a hack a day. The frequency of attacks has roughly doubled in the last six months — from ~7.8 incidents per month last summer to ~15.2 per month through this spring. By the time you finish reading this, several smaller protocols will likely be getting drained somewhere on chain.
This is not a normal cyclical security wobble. The economics of attacking DeFi have structurally shifted, and the high-APY-sketchy-protocol meta — DegenFi — is over. Not because regulators killed it. Because the math stopped working for users.
What’s coming next is the version of this industry that was always supposed to be here: actually decentralized, deliberately constrained, architected to survive an adversarial environment. In Tradfi, centralization is a coordination mechanism that institutions can be held accountable for. On an immutable ledger, where there is no rollback, every centralized control point is something else entirely. It’s an attack surface.
Two Vectors, both AI-accelerated
The acceleration is happening because attacker costs collapsed on two fronts at once.
The Long Tail.
AI agents now scan smart contracts for vulnerabilities at roughly $1.22 per contract, with capability reportedly doubling every 1.3 months. April had 23 protocol-logic exploits — oracle misconfigurations, fee accounting flaws, first-depositor attacks, signature replay, refund logic bugs, fake collateral exploits. These are the kinds of bugs human auditors would catch *if they had time to read every contract on every chain*. They never did. AI agents do. The long tail of DeFi — every small protocol on DeFiLlama — is now under continuous, automated review by attackers. Bugs that survived in obscurity are getting found.
The High End
Nation-state actors, Lazarus most prominently, run months-long social-engineering operations against privileged humans and the infrastructure they control. AI helps here too — better phishing, better impersonation, faster reconnaissance — but the bottleneck remains human patience and access. April delivered Drift ($285M, admin key compromise plus price manipulation), Kelp ($293M, LayerZero OFT bridge exploit), Wasabi Perps ($5.5M, admin key), Grinex ($15M, hot wallet). Five infrastructure failures, $593M.
The split inside April’s data is the cleanest expression of where DeFi’s losses actually come from:
Infrastructure (admin keys, hot wallets, bridges)
5 incidents
$593M lost (93.4% of value lost)
Protocol logic (code bugs, oracles, flash loans)
23 incidents
$42M (6.6% of value lost)
Five infrastructure failures caused 93% of the dollar losses. Twenty-three smart-contract bugs — the things audits are designed to catch — accounted for less than 7%. The frequency story lives at the bottom of the table; the dollars story lives at the top. Neither is going away. Both are accelerating.
The middle of the market — small-but-flush protocols with weak operational security — is the worst place to be. Big enough to be a target, not hardened enough to survive being one.
Centralization as Attack Surface
The reason these attacks succeed at scale is not that any single team is incompetent. The teams being targeted include some of the most capable operators in the space. The reason is structural: in a system without rollback, every privileged control point is a permanent liability — and the more capital sitting behind that control point, the higher the EV for an attacker willing to be patient.
The actual condition that makes a protocol a Lazarus-grade target is the pairing of three things: Centralized control, Centralized liquidity, and Weak guardrails.
Centralized control without much liquidity behind it is a nuisance, not a payday. Centralized liquidity without privileged control points (think a Uniswap pool) has no compromise vector. Either condition with hard guardrails — rate limits, mint caps, timelocks, pause guardians — caps the blast radius. Combine all three, and the math works: a single compromise unlocks a 9-figure prize, with no way to undo it.
April’s losses fit this template precisely. Drift’s price oracle had centralized authority over a large pool. Kelp’s bridge architecture concentrated trust in a small set of validators sitting between meaningful TVL and its mint authority. The protocols weren’t beaten by smart contract bugs; they were beaten by the structural pairing that makes such targets worth six months of nation-state effort in the first place.
This is where DeFi’s relationship with centralization diverges sharply from tradfi’s. Banks can centralize trust because regulators, courts, and FDIC insurance create a rollback mechanism. The system is designed to absorb the inevitable failures of concentrated trust. DeFi has none of that. Every centralized component must be evaluated as a potential point of permanent, irreversible failure. Decentralization isn’t an ideology in DeFi. It’s a security property — and it has to be evaluated alongside liquidity concentration and guardrails to mean anything.
What Survives
Look at what didn’t show up in April’s list. No successful exploits on Uniswap v2 or v3 pools. None on Morpho Blue’s isolated markets. None on Liquity-style minimal-governance designs. The protocols that survive in this environment share a structural pattern, and it’s worth being precise about what that pattern is.
Lindy primitives, not Lindy brands. Age and TVL alone don’t protect anything. Mutable proxy contracts with active governance get re-tested every time governance touches them; the security clock effectively resets with each upgrade. Immutable primitives that have been live for years without changes have been continuously battle-tested against every incentive an attacker has. Uniswap v2 cannot be upgraded, governance cannot list new assets in existing pools, and the risk profile is bounded by construction. That is a fundamentally different security posture than a protocol whose admin keys can change asset listings, risk parameters, or core logic at any time.
Isolated risk, not pooled risk.
Pooled lending designs inherit the security of every asset listed against them, including the full upstream dependency chain of those assets — the bridges they cross, the validators they trust, the off-chain components that mint them. A bad listing affects the entire protocol. Isolated markets, like Morpho Blue’s per-market structure, contain the failure to the specific market that took the bad listing. The same money is doing the same work, but the blast radius of any single failure is dramatically smaller.
Minimal off-chain dependencies. Every off-chain signer, every centralized oracle, every privileged keeper bot is a Lazarus target. Protocols that minimize these — even at the cost of capital efficiency or feature richness — survive the security environment that 2026 has actually delivered.
The bullish read of all this: the environment isn’t killing DeFi. It’s killing the architectures that were always going to fail eventually. What remains is what was supposed to be there from the start.
What to Do about it
The center of gravity for users in this environment is no longer “find the highest APY.” It’s “evaluate the architecture, then size positions to actually-priced tail risk.” Every recommendation below maps to a failure mode the data has already named.
Project selection — architecture beats brand. Investigate admin key setup directly: multisig threshold, signer identities, timelock duration, whether there’s a pause-only guardian, and what powers the keys actually have. Prefer immutable primitives over mutable front-ends with broad asset listings. Look for visible bounty programs, recent audits from reputable firms, and decentralized control. AI tools can help skim docs and audit reports for warning signs — use them.
If you’re building: multisig with pause-only guardians, timelocked admin actions, and minimized privileged off-chain components are table stakes now. The April list is a list of teams that thought their opsec was good enough.*
Risk/reward — make sure the reward is actually compensating you for the risk you take. The implicit tail risk in complex DeFi protocols has risen as base-rate exploit frequency goes up and AI industrializes the attacker side. That doesn’t mean DeFi yields aren’t worth taking — for users who can run good opsec, do real diligence, and monitor positions, the risk-adjusted returns can still be good. It does mean the reward needs to actually price the risk. Use treasury-yield products like Ondo USDY or sUSDS as your reference rate. If a complex protocol is paying you less than treasury yield, you are taking smart-contract risk for negative expected value — exit or rotate. Higher APYs (15%+) can be appropriate for sized positions in protocols that pass real diligence, but the position sizing has to reflect actual survivability, not historical TVL.
Position construction — isolate your exposure. When lending, prefer protocols built on isolated-liquidity architectures over pooled lending. The fully isolated form — a single collateral against a single borrowed asset, as in raw Morpho Blue or Euler v2 markets — is the safest design but typically illiquid and poorly-yielding for retail users, who often can’t realistically navigate them directly. The practical sweet spot is well-curated vaults sitting on top of those primitives: vaults that allocate across multiple isolated markets, lending only against collateral you understand, run by curators with a track record of navigating crisis well. Steakhouse Financial’s vaults on Morpho are a reference point here; Euler’s own DAO-managed vaults often hit a similar balance.
Pooled-lending designs aren’t categorically disqualified — Spark, for instance, runs tight risk tolerances and conservative listings that make its risk-adjusted profile reasonable despite the larger attack surface a pooled model creates — but the bar for trusting a pooled protocol is now meaningfully higher than for an isolated one.
LP positions often have better risk geometry than lending overall: exposure is bounded to the assets you chose, and the payoff for exploiting an LP position is typically lower than draining a money market, which means LPs attract less attacker attention per dollar.
Tranched products can absorb contagion: Yuzu Money’s senior tranche stayed whole when Aave borrow-rate spikes during the Kelp incident pushed underlying strategies into negative carry, with the junior tranche absorbing roughly $170K of drawdown by design. But tranching transfers risk between users; it does not eliminate protocol-level exploit risk. The underlying still has to be sound.
Advanced: borrowing against risky collateral can reduce your exposure to the collateral itself, but adds liquidation and rate risk — only for farmers actively monitoring positions.
If you’re building: isolate liquidity where the design allows, and impose hard guardrails — rate limits, mint caps, timelocks — wherever centralized control exists.*
Diversify out, not just within. If you don’t have time to due diligence and monitor positions, the answer isn’t to hold more DeFi positions. It’s to hold less. Spot, LSDs, Polymarket, RWA exposure — these don’t share the smart-contract-and-key-compromise risk surface that’s currently being industrialized. Treat DeFi exposure as a deliberate allocation to a high-tail-risk asset class, not as a default home for stablecoins.
Opsec — assume you are a target. Hardware wallet minimum. Dedicated signing device for large positions, ideally separate from your daily-driver computer. Tools that show what you’re actually signing — Rabby, GridPlus Lattice. Revoke unused approvals regularly. The same Lazarus operators going after protocol teams are going after individual whales.
If you’re building: make security disclosure cheap. Active bounty programs, clear contact paths, no legal threats against white-hats. The cheapest exploit is the one a researcher reports before the attacker finds it.
DeFi - Only Finance that Survives Onchain
As more tradfi assets come onchain — Treasuries, equities, RWA wrappers — they will inherit the same adversarial environment that DeFi-native protocols are now learning to survive. Tokenized doesn’t mean safe. The wrapper has to be genuinely decentralized in control, isolated in liquidity, and hard-bounded in privilege, or it becomes the next entry on next April’s list.
This is what 2026 is teaching anyone willing to read the data. The era of farming high APY on architectures that never made structural sense is over because the architectures don’t survive the security environment anymore. What remains is real.
Decentralized Finance isn’t a meme. Onchain, it’s the only finance that survives.
-Danger